‘VMware’ Cloud Director Vulnerability Allows 100% Takeover of Corporate Server Infrastructures
Latest vCloud Director vulnerability provides RCE (remote code execution) privilege to hackers. Learn how this was made possible and if we have a vCloud Director fix yet.

On June 1, 2020, a highly critical VMware Cloud Director vulnerability was disclosed to the world, that basically hands over an enterprise server’s keys to the hacker.
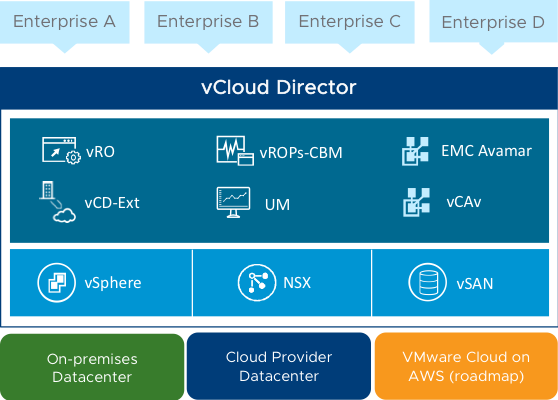
VMware is a popular cloud services corporation, with an abundant range of products and services such as Private Hybrid Cloud Solutions, Hyperconverged Infrastructure, Virtual Cloud Networking, App Virtualization, Storage Technology among others. VMware Cloud Director is one of their most popular services. Originally known as vCloud Director, it is widely used by enterprise level companies and cloud service providers for data center expansion and management, automation, cloud development and migration, multi-site management and more.
But the trusted VMware Cloud Director came under heat when Citadelo, a cybersecurity firm, released a security update detailing how the vCloud Director can be abused to gain privilege access.
VMware Cloud Director Vulnerability Explained
The newly-found VMware Cloud Director exploit was first discovered in April, when the Citadelo team was performing a security audit for an unnamed Fortune 500 client. This enterprise, as clear by now, used VMware Cloud Director and wanted to investigate their cloud infrastructure.
This vulnerability has been rated 8.8 CVSSv3 Score, and classified as CVE-2020-3956.
The root cause of this flaw can be determined as improper handling of the input, resulting in a code injection vulnerability. However, this exploit can only take effect when the input is sent from an authenticated attacker. He can send “malicious traffic” to the VMware Cloud Director, which can subsequently cause arbitrary RCE (Remote Code Execution).
This code injection flaw can be exploited by means of:
- HTML5- and Flex-based UIs
- API Explorer interface
- API access
Researcher leads Tomáš Melicher and Lukáš Václavík further explain the technicality that led them to this finding,
“Everything started with just a simple anomaly. When we entered ${7*7} as a hostname for the SMTP server in vCloud Director, we received the following error message: String value has an invalid format, value: [49]. It indicated some form of Expression Language injection, as we were able to evaluate simple arithmetic functions on the server-side.”
After a few failed attempts, the team was finally able to access arbitrary java classes and call them with malicious payloads.
CVE-2020-3956 Vulnerability Impact
This vCloud Director vulnerability has been regarded as ‘highly important’ because it can allow a skilled hacker to gain full control of the target corporation’s entire infrastructure. The extent of this bug’s devastating effects reach upto the ability of attacker to gain access of:
- All customers within the infrastructure
- Available private clouds,
- Sensitive company and customer information, such as:
- Full names
- Emails
- Password hashes
- IP addresses - Internal system databases for:
- Foreign Virtual machines’ tampering
- Privilege escalation of administrators
- Stealing login credentials
Citadelo ethical hackers behind this discovery have released a POC (Proof of Concept) to exhibit how severe this flaw really is. Click here to check it out.
VMware Cloud Director Patch
Like with most genuine researches, the Citadelo team also privately notified the VMware offices about the said vulnerability and its exploits. VMware development team has released it’s Cloud Director fixes in recent updates.
Vulnerable VMware Cloud Director Versions:
(On Linux and PhotonOS machines)
- <= 10.0.1
- <= 9.7.0.4
- <= 9.5.0.5
- <= 9.1.0.3
Patched Versions:
- 9.1.0.4
- 9.5.0.6
- 9.7.0.5
- 10.0.0.2
Additionally, VMware has also published a Mitigation Workaround on this issue, in their Knowledge base. Click here to go through it.