Yahoo fixes Critical Remote Command Execution vulnerability
Yahoo fixes Critical Remote Command Execution vulnerability
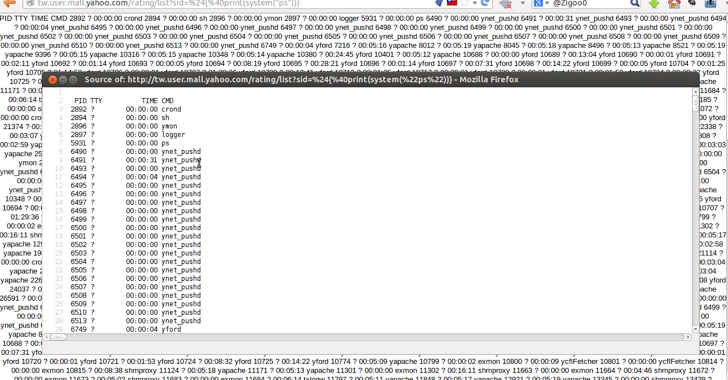
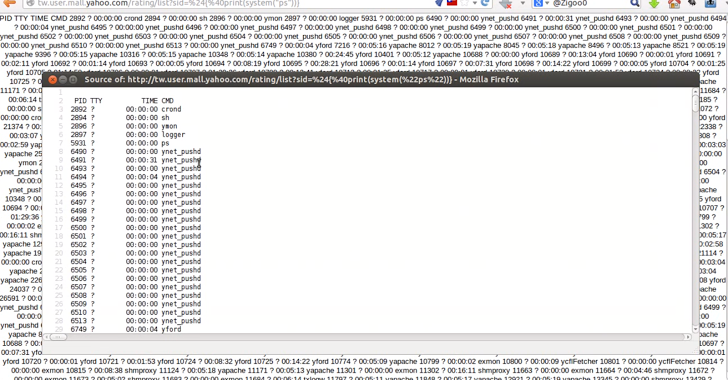
Cyber Security Expert and Penetration tester, Ebrahim Hegazy has found a serious vulnerability in Yahoo's website that allows an attacker to remotely execute any commands on the server i.e. Remote Command Execution vulnerability.
According to Ebrahim blog post, the vulnerability resides in a Chinese subdomin of Yahoo website i.e. http://tw.user.mall.yahoo.com/rating/list?sid=$Vulnerability
Any remote user can manipulate the input to the sid parameter in the above URL, that passes the parameter value to an eval() PHP function on the server end.
If an attacker is able to inject a PHP code into this web application, it forces the server to execute it, but this method only limited by what PHP is capable of.
In a POC Video he has successfully demonstrated few Payloads:
Example-1: http://tw.user.mall.yahoo.com/rating/list?sid=${@print(system(“dir”))}
Example-2: http://tw.user.mall.yahoo.com/rating/list?sid=${@print(system(“ps”))}
Last week, He reported the flaw to Yahoo Security Team and also tip-off them of more threat. Interesting fact, Yahoo has fixed the flaw within a day after he reported.
Server kernel was an old one with a well known “Local Privilage Esclation” vulnerability, which means an attacker with such vulnerability can gain ROOT ACCESS to the server!!!!
Just a few days back, Facebook has also paid out its largest Bug Bounty ever of $33,500 to a Brazilian security researcher for discovering and reporting a critical Remote code execution vulnerability, which potentially allows the full control of a server.